There’s a small window of opportunity for enterprises to lock in discounted prices for three-year Microsoft 365 E3/E5 subscriptions through Cloud Solution Providers like us.
Microsoft is offering a 10% discount on three‑year Microsoft 365 E3 and E5 subscriptions through CSP partners until 30 June 2026. With Microsoft announcing new features across the M365 suites and future price increases, coming in July 2026, this is the perfect moment to lock in lower pricing and secure the enhanced capabilities coming to the platform at a discounted rate.
As an existing Microsoft 365 E3 customer, you already benefit from the essential productivity tools and the baseline security and management capabilities needed to support a secure, modern workplace.
E3 delivers:
Microsoft 365 E5 builds on your current E3 foundation by adding Microsoft’s most advanced, AI‑powered security, compliance, and analytics capabilities.
What E5 adds today:
Microsoft is expanding E5 in 2026 with powerful new capabilities, including:
These enhancements substantially increase the long‑term value of an E5 upgrade, especially for organisations modernising security or consolidating third‑party tools.
Microsoft resource: Compare Microsoft 365 E3 and E5 side by side
Until 30 June 2026, Microsoft is offering a 10% discount on Microsoft 365 E3 and Microsoft 365 E5 under a three-year commitment when purchased through a CSP. There are precise terms and conditions governing eligibility and pricing around this promotion:
The value of this offer is straightforward: commit to Microsoft 365 E3 or Microsoft 365 E5 for three years and benefit from reduced pricing. What makes it meaningful, though, is the stability: a three-year term provides cost predictability, enabling you to budget confidently. It also creates a stable IT environment for any multi-year security, compliance, or modernisation initiatives you may pursue.
If you’re thinking about standardising on Microsoft 365 or strengthening its security capabilities, this is a good time to make that move and lock in an E3 or E5 plan that supports your long-term business goals.
Question 1 | We already have Microsoft 365. Do we qualify for this promotion?
It depends on which SKU you currently hold. This promotion is new-to-offer only, meaning you cannot have prior purchase history of the specific SKU you’re seeking to discount. For example, if you have Microsoft 365 E3 today, you would not qualify for the E3 promotional discount – but you may qualify for the E5 promotional discount if you have not previously purchased that SKU.
Question 2 | We have more than 9,999 users. Can we still participate?
Yes – but the promotional pricing applies to the first 9,999 licences per SKU only. Licences above that threshold are purchased at standard list pricing. For large enterprises, this still represents meaningful savings on a substantial portion of the Microsoft 365 E3/E5 licensing footprint.
Question 3 | What if our headcount changes during the three-year term?
Three-year subscriptions through the CSP programme allow licence additions during the term, but do not allow licence reductions. Enterprises with stable or growing workforces are best positioned for this structure. If your headcount fluctuates significantly, then a hybrid approach – committing a baseline on three-year terms and covering variable licences on annual or monthly terms – can be an effective strategy.
Microsoft 365 licensing decisions influence architecture, risk posture, and operational cost. They shouldn’t be made in isolation.
As a CSP and Microsoft Solutions Partner for Microsoft Cloud, we approach Microsoft 365 engagements from a consultative and technical perspective. We assess your current licensing and security setup, regulatory exposure, and any third-party tool overlap before making recommendations for your enterprise. Our experts can provide:
The CSP promotion is available until 30 June 2026. While that may seem distant, licensing transitions, security evaluations and procurement cycles often require careful planning. If you’re considering a move to Microsoft 365, evaluating an upgrade from E3 to E5, or planning your renewals for the year, now’s the time for a structured review of your licensing strategy.
Let us walk you through the Microsoft 365 options most relevant to your enterprise and help you take advantage of the CSP promotion while it lasts. Complete the form below to schedule a Microsoft 365 E3 or Microsoft 365 E5 licensing consultation with our team.
BUI is supporting Data Privacy Week as a Champion organisation, promoting transparency, trust, and practical steps to help you take control of your personal data.
BUI is proud to announce its commitment to Data Privacy Week 2026, taking place from 26-30 January, by registering as an official Data Privacy Week Champion.
As a Champion organisation, BUI recognises and supports the principle that all organisations share the responsibility of being conscientious stewards of personal information. In an era where data is generated constantly (often without people even realising it), respecting privacy is a fundamental component of trust.
Data Privacy Week is a global awareness initiative led in North America by the National Cybersecurity Alliance. Originally launched as Data Privacy Day, the campaign has expanded into a full week to reflect the growing importance of privacy in our always-connected, data-driven world.
The goal of Data Privacy Week is twofold: to help individuals understand that they have power and choice over their personal data, and to help organisations understand why respecting data privacy is essential to maintaining transparency and accountability.
Today, data privacy is about much more than screen-locking and device security. It includes how information about us – our identities, locations, behaviours, and preferences – is collected, managed, and protected online. At its core, data privacy is about our right to decide how much of our personal information is visible, accessible, or shared – and with whom.
When we browse a website, stream a video, or use a mobile app, we’re generating vast amounts of information about ourselves and our habits. This data is valuable and often monetised by service providers, advertisers, and data brokers – even when it’s claimed to be anonymised.
This year, Data Privacy Week highlights the growing expectation that organisations treat privacy as a core value rather than a compliance exercise, notes BUI Group Governance and Compliance Manager Dhiren Boodhia. “Every organisation that handles personal information has a duty to be deliberate about how that data is collected, used, and secured. Data Privacy Week is an opportunity to pause, reflect, and make sure those decisions are being made with people top of mind,” he says.
While it’s difficult to control how each byte of data about you is processed, you are not powerless. Data Privacy Week is all about taking practical steps to manage your personal information.
When you download a new app, create an online account, or sign up for a digital service, you’re often asked to share personal information before you can even get started. This might include access to your location, contacts, photos, or data about how you use your device.
For the organisations offering “free” services, personal data is often a key part of the value exchange. That doesn’t mean you should automatically say no – but it does mean it’s worth pausing to assess whether the service you’re getting is a fair return for the data being requested. One way to approach these decisions is to think about necessity. Ask yourself:
Once you understand this trade-off between privacy and convenience, it becomes easier to make smarter choices about your data – and often, you can still use digital apps and services while sharing far less information than you initially thought necessary.
Most apps and digital services include privacy and security settings that let you manage how your personal information is used. These settings usually only take a few minutes to review, but they’re often overlooked.
Even if an app or service doesn’t actively ask for certain data, it’s safest to assume it may still be collecting information in the background. That’s why it’s a good idea to review your privacy settings regularly to make sure they still reflect your level of comfort.
As a starting point, consider turning the following permissions off unless they’re essential and you trust the app or service:
You don’t need to review everything at once. Start with one device or a handful of apps, and build the habit over time. Regular check-ins can make a meaningful difference to how much data you share.
Strong security habits help ensure that your personal information doesn’t fall into the wrong hands, whether through account compromise, malware, or social engineering. Along with managing your data privacy settings, remember these tips to safeguard your information:
Together, these habits can help protect not just your data, but your digital identity as a whole.
Throughout Data Privacy Week, we’ll be sharing tips and resources to help you become more aware of data privacy at work, at home, and on the move. Follow us on Facebook and LinkedIn and join the conversation by using the #DataPrivacyWeek hashtag online.
Data Privacy Week began as Data Privacy Day in the United States and Canada in January 2008 as an extension of the Data Protection Day celebration in Europe. Data Protection Day commemorates the 28 January 1981 signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection. The National Cybersecurity Alliance, the United States’ leading non-profit, public-private partnership promoting cybersecurity and privacy education and awareness, leads the effort in North America each year. For more information, visit www.staysafeonline.org/data-privacy-week/.
The National Cybersecurity Alliance (NCA) is a non-profit organisation on a mission to create a more secure, interconnected world. The NCA advocates for the safe use of all technology and educates everyone on how best to protect themselves, their families, and their organisations from cybercrime. The NCA creates strong partnerships between governments and corporations to amplify its message and to foster a greater digital good. For more information, visit www.staysafeonline.org.
Here’s how BUI can help you take advantage of the new AI-powered capabilities in Microsoft Defender, Microsoft Sentinel and Microsoft 365 E5 to strengthen your security operations.
The security landscape is shifting again: Microsoft has just unveiled a new wave of integrated AI capabilities across Microsoft Defender, Microsoft Sentinel and Microsoft 365 E5. These advancements, showcased during the 2025 Microsoft Ignite conference in San Francisco, are designed to transform how organisations detect, investigate and respond to threats. For those already managing complex hybrid and multi-cloud environments, this new era of AI-powered security offers substantial benefits – but it also requires a strategic approach to deployment and implementation to ensure success.
As a Microsoft Solutions Partner for Security, a Microsoft MXDR Verified Partner, and a member of the Microsoft Intelligent Security Association, we’re uniquely positioned to help you turn these innovations into measurable results. Let’s take a closer look at the major security announcements from Ignite, what they mean for organisations like yours, and how the BUI team can support you.
Microsoft has introduced new agents, powered by Security Copilot, to bring AI into the day-to-day workflows for SIEM and XDR users within Microsoft Defender. These agents can assist with threat hunting, intelligence analysis, incident investigation, and risk prioritisation, helping analysts work faster and more accurately. Microsoft is also improving the Microsoft Defender incident queue, with an updated AI-powered experience now in public preview.
Quick overview: The Threat Hunting Agent guides analysts through end-to-end investigations using natural language. It delivers direct answers, suggests investigative steps, and provides context that speeds up the discovery of anomalies.
Key benefits: With this agent in play, threat hunting becomes faster and more consistent. Your junior analysts will be empowered to perform advanced tasks and your senior analysts will gain precious time for deeper analysis. Overall, your SecOps team will benefit from increased investigative capacity.
Quick overview: Integrated into the Microsoft Defender portal, the Threat Intelligence Briefing Agent creates custom intelligence briefings by combining Microsoft Threat Intelligence with global feeds and organisation-specific context. Analysts can use these briefings to better understand risks, vulnerabilities, and emerging campaigns.
Key benefits: Your SecOps team will gain quick access to relevant threat intelligence without having to conduct manual research. They can prioritise risks more effectively and initiate remediation based on clear recommendations and direct links to affected assets.
Quick overview: The Dynamic Threat Detection Agent proactively hunts for false negatives and blind spots. When a major incident occurs, it checks for related undetected threats (such as latent activity on sensitive identities), thereby identifying gaps that traditional alerting might miss.
Key benefits: Your SecOps team will have a safety net that increases confidence during high-impact investigations. You’ll be able to validate that incidents have been fully contained and that hidden activity does not go unnoticed.
Quick overview: A new Microsoft Defender incident queue experience (currently in public preview) uses artificial intelligence to score and prioritise security incidents. By leveraging factors like alert types, criticality tags and MITRE mappings, it produces risk scores that help analysts understand which incidents require immediate action.
Key benefits: Your SecOps team will have a clear view of incident rankings, enabling faster and more confident decision-making in the face of high-impact threats.
Microsoft has also introduced a significant set of updates to Microsoft Sentinel, its connector ecosystem, and the Sentinel data lake. Together, these improvements support businesses that want to unify signals, reduce storage costs, and maintain strict governance across complex cloud environments.
Quick overview: Microsoft unveiled a broad set of new out-of-the-box connectors that support AWS, GCP, SAP, Palo Alto and numerous third-party security and compliance platforms. These connectors make it easier to bring multi-cloud and hybrid telemetry into Sentinel without custom development.
Why this matters: Richer telemetry increases the accuracy of detection and reduces blind spots across your distributed environments. These connectors also expand Microsoft Purview Data Security Posture Management capabilities through streamlined access to external data asset information.
Quick overview: Sentinel now supports the direct ingestion of Microsoft Defender for Endpoint data into the data lake, with Defender for Office 365 and Defender for Cloud Apps expansion coming in December 2025. Entra, Syslog, CEF and CommonSecurityLog sources can also be ingested.
Why this matters: This model gives you cost-effective long-term storage for historical security data. It also provides the depth needed for retro-hunting, incident review, and compliance without storing everything in the analytics tier.
Quick overview: The Sentinel data lake has enhanced its permission model to enable users to access workspace data in the lake based on their granular Azure role-based access control (RBAC) permissions on each workspace. Support for managed identities and service principals is coming soon.
Why this matters: You can now implement more precise access controls, supporting least-privilege models across your SIEM and data lake environments. Your automation workflows can also operate more securely through identity-based access.
Quick overview: Microsoft’s threat intelligence library covering threat actors, vulnerabilities, campaigns, and indicators of compromise is now available to Sentinel users. The intelligence aligns to MITRE techniques, tactics and procedures.
Why this matters: High-quality threat intelligence gives analysts detailed insights for proactive hunting and remediation. Your SecOps team can respond more effectively when attacker behaviours and relevant indicators are clear.

Ryan Roslansky (CEO, LinkedIn and Executive Vice President, Microsoft Office and Copilot) speaks during the 2025 Microsoft Ignite conference in San Francisco. Photo credit: Microsoft
One of the most impactful Ignite announcements this week was the inclusion of Security Copilot for Microsoft 365 E5 customers. This change brings AI agents directly into Defender, Entra, Purview and Intune for Microsoft 365 E5 customers.
Quick overview: Security Copilot capabilities are being activated for Microsoft 365 E5 customers in phases. Organisations with existing Security Copilot licences and Microsoft 365 E5 have access now. All other Microsoft 365 E5 customers will receive access soon, with a 30-day advance notification from Microsoft.
Why this matters: For many organisations, this significantly increases the value of their Microsoft 365 E5 investments, especially at a time when staff shortages and high alert volumes are putting pressure on internal teams. Now, SecOps analysts will gain immediate access to AI tools across the Microsoft 365 security ecosystem for richer context and consistent, intelligent assistance.
The latest AI capabilities in Microsoft Defender and Microsoft Sentinel allow security professionals to work faster and more accurately, but only when they’re properly embedded into existing processes. We can help you:
Whether you’re onboarding new data sources, expanding your threat intelligence workflows, or modernising your architecture, we can provide the technical and operational support to transform your Security Operations Centre into a proactive, intelligence-driven defence hub.
With Security Copilot now included for Microsoft 365 E5 customers – and Security Compute Units (SCUs) required to scale AI workloads – you may need clarity on configuration, optimisation, and cost control. We provide guided deployment and optimisation services to help you verify that Security Copilot is configured correctly; prompts and workflows are efficient; and SCU usage remains predictable. We can also help you model and forecast usage patterns so that you gain maximum value without unnecessary spend.
As AI becomes more important to your security operations, you’re responsible for ensuring that automation remains transparent, validated, and aligned with applicable compliance policies. We can help you establish practical oversight frameworks that support the confident use of AI. Our advisory services include governance model design, automated action review, validation of AI-assisted outcomes, and guardrails that reduce risk while maintaining agility. This approach enables your team to innovate securely while retaining full control and accountability.
Microsoft Ignite 2025 has made one thing undeniable: AI is now at the core of Microsoft’s security stack, empowering organisations with smarter detection, richer context, and automated decision-making across Microsoft Defender, Microsoft Sentinel, and Microsoft 365 E5.
Here at BUI, we know that adopting new technologies is only the beginning… The real business transformation happens when AI is operationalised: integrated into playbooks, governed responsibly, and fully embraced by the people who depend on it.
We’re here to help. If you’re ready to strengthen your security posture, modernise your security operations, and empower your teams with Microsoft’s latest capabilities, let’s get started. Contact us to arrange a chat.

Zandre Janse van Vuuren explains why cybercrime spikes during the holiday season and shares practical tips to help you protect your organisation from opportunistic attackers.
By Zandre Janse van Vuuren | Service Delivery Manager: Cyber DFIR, BUI
The months of November and December are a perfect storm for cybercriminals. Retailers, logistics companies, and organisations closing out their financial year are at peak operational intensity, processing high volumes of sales, payments, and customer data.
But just as business activity surges, security staffing drops. Key personnel take annual leave, incident response teams shrink, and IT capacity thins out. This imbalance creates what’s known as the “holiday blackout”, a seasonal window when attackers know defences are down and reaction times are slow.
During this period, cybercriminals ramp up their ransomware, phishing and extortion campaigns to strike when you’re least prepared. And their goal isn’t just to breach your defences: it’s to disrupt your operations when downtime is most damaging.
The solution? In a word: readiness. By focusing on cyber resilience (your ability to protect your critical assets, respond to inevitable attacks, and recover quickly), you can keep your business running and reduce the risk of financial and reputational damage when attackers do strike.
The holiday season brings an uptick in cybercrimes and digital scams that exploit distraction, emotion, and urgency. Understanding this threat landscape is essential for developing a proactive security strategy for your organisation.
Phishing is consistently identified as the number one social engineering strategy. During the holiday season, cybercriminals know that people are juggling personal shopping, shipping alerts and end-of-year workplace tasks, which lowers vigilance and increases click rates. Common phishing campaigns include:
When inboxes and screens are flooded with legitimate notifications, a fake one can slip through easily – especially when employees are too stressed or too distracted to stop and interrogate a suspicious message.
Behind many of these phishing campaigns are access brokers who specialise in gaining unauthorised initial access to organisational networks and then selling that access to ransomware groups. There’s typically a surge in access-broker activity at the end of the year when networks are busy, oversight is reduced, and employees are overwhelmed with tasks at home and at work. Successful breaches often become the entry point for larger ransomware attacks that unfold over the holidays.
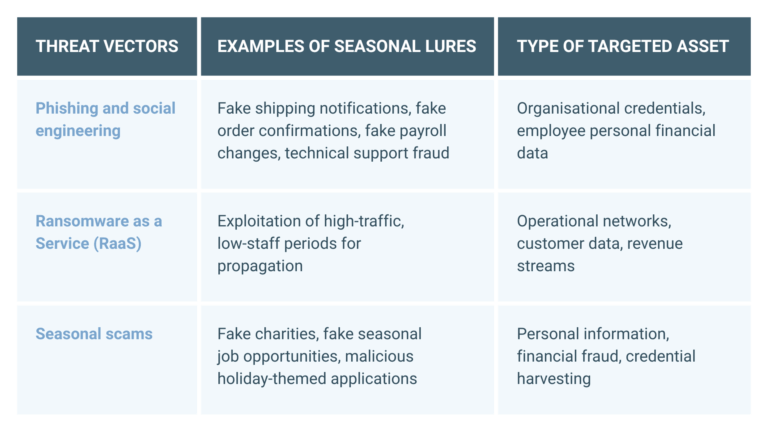
Table: Threat vectors that organisations must prepare for during the holiday season
The biggest enabler of seasonal cybercrime is reduced security staffing. Attackers time their strikes for weekends, public holidays and vacation periods, knowing that organisations are at their most vulnerable. Industry research highlights the risk clearly:
Meanwhile, modern cyberattacks move quickly: it often takes less than an hour from the moment a user clicks on a malicious link until the attacker establishes a firm foothold in the system. When critical security personnel are unavailable, alerts may go unread for hours or even days, giving attackers free rein. The risk isn’t just slower detection; it’s complete operational paralysis until normal staffing resumes. That’s why seasonal security planning should prioritise rapid response capability, not just detection.
Cyber resilience requires more than robust technical defences and safeguards: it demands a strategic mindset. At the very least, you should:
Don’t ever think you’re too small to be targeted. It’s a myth that cybercriminals ignore startups and micro- and medium-sized businesses. Smaller organisations like these are prime targets precisely because they likely have fewer defences. Remember, cybercrime has been industrialised: attackers sell stolen credentials and exploitative tools on the dark web, enabling virtually anyone to target any company’s digital assets.
Legacy or unpatched systems can be easy entry points for cybercriminals – and once they’re in, they can take advantage of existing vulnerabilities, flaws, and weaknesses in your environment. If you’ve neglected your systems and become lax about your security, then a single breach could snowball into a catastrophic business failure. Make sure you concentrate on patching and protecting your systems before key security staff go on vacation.
Robust identity and access management controls and device encryption are essential throughout the year – but even more so during the holiday season when security teams are smaller and more pressured. Make sure you enforce strong password policies and encrypt all sensitive data (at rest and in transit) to help prevent data leaks in the event that business devices are mishandled, lost, or stolen.
A written incident response plan isn’t good enough; it needs to be tried and tested. Many organisations still haven’t rehearsed what to do if a ransomware attack occurs over a weekend or holiday period. Make sure you’ve run tabletop exercises, tested communications and capabilities under low-staff conditions, and confirmed that everyone knows their role.
Human error remains the top cause of breaches. Take the time to give your employees a refresher course in password hygiene, general security awareness and vigilance, and the correct technical route for raising and reporting issues. Regular mini training sessions that address the current threat landscape (for example, a 10-minute overview of seasonal phishing tactics) can be more effective than lengthy presentations.
Cyber resilience means having a framework that protects your key assets, enables an effective response, supports quick recovery, and maintains customer trust even after a successful cyberattack. Building this framework involves assessing risks, keeping hardware and software updated, reviewing access policies, and enforcing security standards across your connected environment.
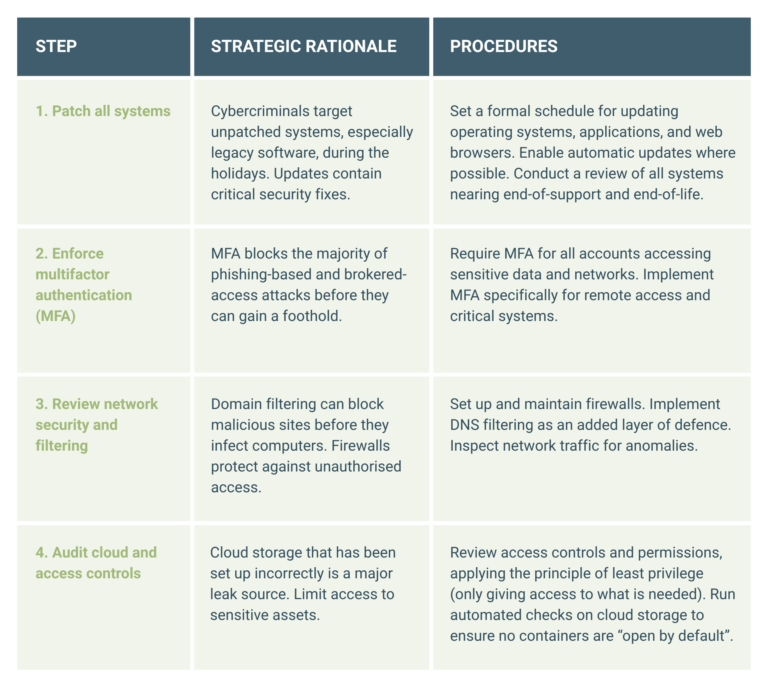
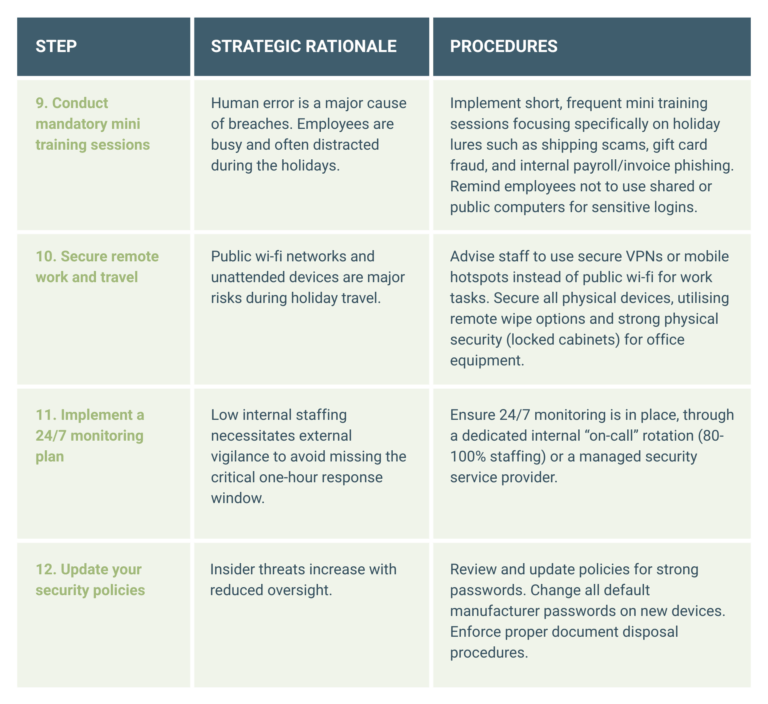
A phased, actionable checklist is necessary to translate strategic goals into measurable operational tasks. This checklist outlines the actions with the highest impact, organised by deployment priority, leading up to the end-of-year shutdown.
Data-recovery capabilities are paramount over the holiday season because a cyberattack during low staffing risks permanent data loss. Your focus must be on assuring restorability rather than merely assuming backups exist.
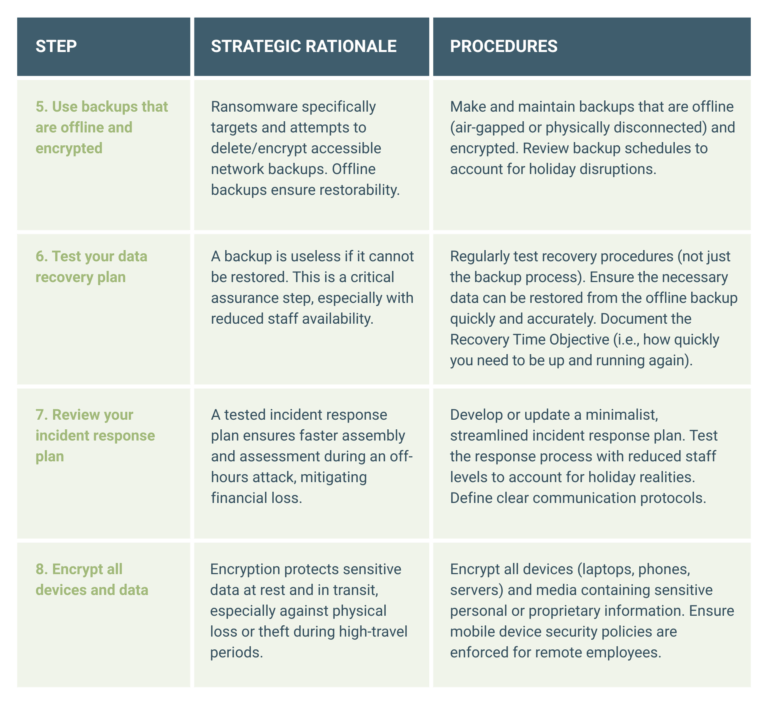
The final week should be focused on staff education so that your people are aware of the heightened risk landscape and the prevalence of seasonal scams.
The weeks leading up to the holidays present one of the most dangerous periods of the year for cyberattacks. Well-organised threat groups know that yearend pressures, reduced staffing, and increased digital activity create ideal conditions to strike.
Preventing every attack isn’t realistic, but ensuring your business can withstand, respond to, and recover from one absolutely is. True cyber resilience means being ready for disruption, but this resilience isn’t built overnight: it’s achieved through deliberate preparation, tested plans, and continuous learning.
As the festive season approaches, take the opportunity to validate your defences. Run your incident response plan under reduced staffing conditions. Test your offline backups. Confirm that your recovery strategy actually works when key personnel are away.
The threats of the holiday period are predictable – and that makes them preventable. By being proactive now, you can protect your systems, your data, and your business reputation to ensure a smooth start to the new year.
Cyber threats evolve constantly and your security strategy has to keep up. If you want expert guidance, improved detection capabilities, or help building operational resilience, reach out to our security team and we’ll guide you forward. Get started today.
Heinrich Wewers and Satish Sunker unpack how Microsoft Defender for Cloud can help IT leaders improve cloud security posture, detect threats, and simplify compliance.
Cloud adoption continues to accelerate faster than many organisations’ ability to secure it. As workloads span Microsoft Azure, on-premises environments, and other cloud platforms such as AWS and Google Cloud, the attack surface increases, misconfigurations multiply, and visibility often diminishes.
For CISOs and IT leaders, this creates a fundamental challenge: how do you maintain consistent security and compliance across an ever-changing cloud estate?
“Unified protection is now at the heart of modern cloud security strategies,” says Heinrich Wewers, Senior Cloud Consultant at BUI. “The focus has shifted from securing perimeters to safeguarding identities, configurations and workloads wherever they reside. It’s a reality that makes Microsoft Defender for Cloud an indispensable tool in any defender’s kit.”
Microsoft Defender for Cloud is a unified platform for monitoring and improving the security posture of all cloud resources. It combines Cloud Security Posture Management (CSPM) with Cloud Workload Protection Platform (CWPP) capabilities. CSPM continuously assesses cloud configurations, identifies risks, and delivers actionable recommendations to prevent gaps, while CWPP protects live workloads such as virtual machines, containers, databases, and storage from active threats. Together, these capabilities provide a layered defence across the entire cloud estate.
“Microsoft Defender for Cloud gives you a single-pane-of-glass view across Azure, AWS, Google Cloud, and even on-premises systems,” Wewers explains. “It doesn’t just alert you to problems; it tells you how to fix them and, in many cases, automates the process.”
Microsoft Defender for Cloud integrates natively with Azure and extends protection to other clouds via built-in connectors. This unified approach enables the management of cloud infrastructure and workload security from a single interface, giving security teams consistent visibility and control without having to juggle multiple tools or dashboards.
Traditional perimeter-based security models are no longer effective in the dynamic and distributed nature of modern cloud environments: CISOs must secure virtual machines, identities, containers, databases, and APIs that expand and contract in real time. “Legacy tools lack visibility across multiple clouds. They also lack context awareness of cloud-native constructs and the automation needed for real-time detection,” observes Wewers. “Cloud security today is dynamic, identity-centric, and API-driven.”
In this landscape, many security incidents stem not from advanced zero-day exploits but from everyday misconfigurations and human errors. Problems such as excessive permissions on identities or service principals, missing endpoint protection on cloud VMs, and unmonitored configurations created during rapid deployment can all leave critical resources exposed, says Wewers.
Cloud Security Posture Management platforms such as Microsoft Defender for Cloud address these problems by delivering continuous visibility into cloud assets and their security status; applying baselines mapped to standards such as NIST to ensure consistent compliance; and prioritising remediation efforts by identifying which misconfigurations or vulnerabilities pose the highest risk.
“Cloud security posture management isn’t a one-time exercise,” Wewers emphasises. “It’s an ongoing process. Microsoft Defender for Cloud enables teams to spot risky configurations early on and prevent gaps from accumulating in the dark.”
At the core of Microsoft Defender for Cloud’s posture management is continuous assessment, a constant evaluation of your cloud resources against Microsoft security benchmarks and global standards. Secure Score is the metric that brings this to life, explains Satish Sunker, Cloud Solutions Architect at BUI. “It continuously evaluates your Azure and multi-cloud resources against best practices and compliance standards. Each recommendation (such as enabling multi-factor authentication or restricting network access) carries a weighted impact score. As you implement the recommendations, your Secure Score improves, visually showing your progress toward a stronger security posture.”
Most organisations begin their journey with a Secure Score between 25% and 45%, depending on cloud maturity, Sunker shares. After remediating foundational issues, such as open management ports, unencrypted storage, and missing endpoint protection, many achieve 70% to 85% within months (indicating a well-hardened and monitored environment).
“Secure Score is an evidence-based, real-time metric that helps security teams prioritise actions with the biggest impact on risk reduction. Here at BUI, our customers consistently tell us that they value the contextual guidance, which turns a long list of findings into an actionable road map,” he adds. “Secure Score has also become a KPI for CISOs because it’s quantifiable, easy to track over time, and bridges the communication gap between technical teams and business stakeholders.”
When Microsoft Defender for Cloud identifies risks, it doesn’t just report them: it actually tells you how to fix them. Sunker explains that remediation is intentionally straightforward: “Each recommendation links directly to the affected resource and includes guided or automated ‘fix’ actions. You can enable Just-In-Time VM access with one click, deploy Defender for Servers agents across subscriptions automatically, or apply policies through Azure Policy for long-term prevention.”
This built-in automation lowers the barrier to action, allowing even lean security teams to make meaningful improvements quickly. And because Microsoft Defender for Cloud integrates tightly with Microsoft Sentinel and Logic Apps, many of these remediations can be orchestrated automatically, turning what used to be manual tasks into continuous protection workflows.
Microsoft Defender for Cloud actively detects and responds to cloud-native threats. It identifies malicious activity such as brute-force or anomalous login attempts, suspicious data exfiltration from storage accounts, malware and crypto-mining activity on workloads, SQL injection and privilege escalation in PaaS services, lateral movement between cloud resources, and much more.
Because it’s backed by Microsoft’s global threat intelligence and AI models, threat detection is highly contextual and continuously improving. In many real-world scenarios, BUI has seen this integration prevent incidents from escalating, says Sunker, providing an example. “Microsoft Defender for Cloud might flag anomalous network behaviour on a VM, while Microsoft Sentinel correlates that with a suspicious Entra ID login. That correlation allows our Cyber SOC analysts to stop lateral movement before compromise spreads.”
Regulatory frameworks such as ISO 27001, NIST, GDPR, and SOC 2 increasingly demand continuous, evidence-based compliance. Sunker notes that organisations are expected to prove continuous compliance, not just once-off compliance at audit time. Microsoft Defender for Cloud’s Regulatory Compliance Dashboard simplifies this task dramatically. It maps your configuration and control data against each framework’s requirements in real time, providing comprehensive visibility and insights for auditors and security teams alike.
“Compliance reporting used to involve manual audits and spreadsheets,” says Sunker. “Now, evidence is always current and exportable. You can even customise your compliance initiatives to match internal or industry-specific standards.”
Microsoft Defender for Cloud caters for the fact that most enterprises operate across multiple platforms. Using native connectors and Azure Arc, organisations can extend visibility and policy enforcement beyond Microsoft Azure to AWS, Google Cloud, and on-premises servers. This allows security teams to apply a single set of policies across all clouds, monitor non-Azure workloads in the same dashboard, and use Defender’s threat detection for AWS EC2, Google Cloud Compute Engine, and Kubernetes clusters.
“Hybrid and multi-cloud environments require consistent security controls,” notes Sunker. “Microsoft Defender for Cloud reduces fragmentation and provides a single source of truth for your posture.”
Wewers highlights that Microsoft Defender for Cloud doesn’t operate in isolation. “It’s a foundational component of the broader Microsoft security ecosystem.”
“This ecosystem integration allows for end-to-end visibility, from detection through investigation to remediation,” Wewers notes. “It turns Microsoft Defender for Cloud into a strategic control plane for security across the entire Microsoft security landscape and beyond.”
As organisations continue to evolve their digital strategies, cloud security posture management will remain a critical pillar of resilience, says Wewers. Microsoft Defender for Cloud offers not just visibility, but the intelligence and automation needed to stay ahead of threats in an ever-changing landscape. By unifying assessment, protection, and compliance under one platform, it enables security teams to move from reactive defence to proactive, strategic risk management.
“The most secure organisations are the ones that understand their security posture and continuously strive to improve it. Microsoft Defender for Cloud gives CISOs the clarity and confidence to do just that, across Azure and every connected environment,” he concludes.
To make the most of Microsoft Defender for Cloud, many organisations choose to partner with a certified Azure Expert MSP. Working alongside seasoned specialists ensures that the tool is deployed and tuned effectively, delivering measurable improvements in security posture and compliance. If you’re ready to begin, we’re here to help. Contact the BUI team today.
Jeffrey Fowels explores how organisations can bring AI into their cloud environments and what it takes to turn early experiments into lasting business value.
By Jeffrey Fowels | Cloud Solutions Architect, BUI
Artificial intelligence is no longer a distant promise: it’s reshaping how we work and how organisations operate right now. Over the past few years, this shift has accelerated dramatically as AI has moved from being an interesting experiment to a strategic necessity.
And yet, for many companies, the real question isn’t whether to embrace AI, but rather how to do so effectively and responsibly. This is where I believe Microsoft is changing the game. With tools such as Azure OpenAI and Microsoft Copilot, businesses can bring AI directly into their cloud environments, protected by enterprise-grade security, privacy and compliance.
For companies already invested in the Microsoft ecosystem, this moment represents something powerful: the ability to integrate AI seamlessly with their own data, applications and workflows safely and at scale.
Microsoft Azure has evolved in remarkable ways. In its early days, the focus was on running workloads in the cloud, providing scalable infrastructure and platforms through Infrastructure-as-a-Service and Platform-as-a-Service models. That alone was transformative. But today, Azure has become something far more intelligent: a cloud that doesn’t just host workloads, but actively learns from them.
Azure’s evolution into an intelligent cloud has been built on foundational services like Azure Machine Learning and Cognitive Services, which introduced speech and language capabilities long before generative AI became mainstream. These early building blocks set the stage for what we’re seeing with Azure OpenAI Service, a platform that brings reasoning, prediction and creativity directly into applications and workflows.
This shift has changed how we design cloud strategies. It’s not just about where data lives anymore, but how it can be used intelligently to drive outcomes. Data pipelines, model management, observability and governance are now central to a modern cloud architecture.
The current AI landscape is being shaped by three powerful forces: generative AI, automation, and data-driven decision-making. Together, they’re redefining what’s possible for organisations of every size, in every industry.
Employees now expect tools that help them work smarter and faster, while leaders want deeper insights and better results. The appeal of AI is clear, it delivers measurable value in increasing productivity, reducing costs and unlocking new business models that didn’t even exist a few years ago.
What’s changed most dramatically is the level of maturity. AI adoption began with small proof-of-concept projects (like chatbots), but it’s quickly evolved into enterprise-scale automation and intelligence embedded directly into applications. The conversation has moved from “What is AI?” to “How do we operationalise AI securely?”
Of course, the journey isn’t always straightforward. Many organisations struggle with data quality, compliance, and uncertainty about where to begin. Azure helps overcome these challenges by providing secure data services, responsible AI frameworks and governance tools that keep innovation safe and accountable.
But in my view, the biggest success factor isn’t technology, it’s culture. AI adoption succeeds when policies are clear, when people are empowered, and when teams trust the tools that they use.
One of the most significant developments in Azure’s evolution is the Azure OpenAI Service. It gives organisations secure, enterprise-grade access to advanced AI models such as GPT-4, Codex and DALL-E, all hosted within the trusted Azure environment.
These models enable natural language understanding, content generation, coding assistance, and even image creation but with the governance and data protection that enterprises require. Azure OpenAI ensures that data remains within the organisation’s own Azure tenant. All requests are processed under the customer’s security boundaries, with strict privacy controls and no data shared with external systems.
The real magic happens when Azure OpenAI is connected to a company’s own data using Retrieval-Augmented Generation, combined with Cognitive Search or Azure AI Studio. This creates intelligent assistants that can answer questions and generate insights from internal knowledge bases, accurately and securely.
The most common use cases I’ve seen include:
Azure’s built-in integrations (such as Entra ID for identity, Key Vault for secrets, Private Link for network isolation, and Purview for compliance) enable organisations to innovate confidently while keeping their data secure. And the outcomes are tangible: faster workflows, reduced manual effort, and measurable productivity gains.
While Azure OpenAI enables deep customisation, Microsoft Copilot brings AI to the people, right where they already work. Copilot integrates directly into tools like Word, Excel, Outlook, Teams, GitHub and Dynamics 365, acting as a digital co-worker that assists with the tasks most professionals find time-consuming: drafting content, analysing data, summarising meetings, and automating repetitive processes.
The impact has been profound:
All these Copilots are powered by Azure OpenAI models and Microsoft Graph data, which means they operate inside an organisation’s existing compliance and access controls.
What’s exciting is how these two approaches, Azure OpenAI for customisation and Copilot for everyday use, complement each other perfectly. Azure OpenAI allows developers and architects to build bespoke solutions tailored to specific data and processes, while Copilot democratises AI, making it accessible to everyone.
The feedback we’ve received from organisations adopting Copilot has been overwhelmingly positive. In the months ahead, I fully expect Copilot to become more context-aware, more domain-specific, and more deeply integrated across business and industry workflows as Microsoft further refines the technology.
For organisations looking to get started, bringing AI into your cloud doesn’t have to be overwhelming. A step-by-step approach helps you deliver measurable outcomes safely and efficiently.
Start by choosing a project that is both achievable and measurable, such as summarising documents, automating customer support or enabling internal knowledge search. Then, ask yourself a few checkpoint questions:
By starting small, you can build trust, momentum, and a proof point that sets the tone for scaling.
Data is the fuel for AI and when it comes to generative and predictive workloads, the readiness of your data often determines success or failure. Make sure that you:
Proper data preparation ensures your AI models perform reliably and ethically.
A prototype (or minimum viable AI solution for your particular business challenge) helps prove value quickly, engage your users, and reveal technical hurdles. My suggestions:
A well-executed, successful prototype builds internal credibility and reveals what scaling will require.
Don’t be tempted to skip foundational controls. Make sure you’re proactive about including security and governance protocols from the beginning:
Embedding these controls at the start avoids costly rework later and ensures compliance.
AI is powerful, but it must be used responsibly. That means ensuring trust, fairness, transparency, and accountability across your AI-driven processes. Common best practices:
Remember, responsible AI isn’t an optional nice-to-have: it’s foundational for trust.
Once your pilot is successful, the next challenge is expanding the AI solution across departments, extending its scope, integrating more data, and moving to production. Here are some scaling considerations to bear in mind:
Scaling thoughtfully turns early wins into enterprise-grade capabilities that transform operations.
Moving forward, every organisation must make a choice: observe the AI transformation from the sidelines, or take an active role in shaping how it drives value across the business. Azure OpenAI and Microsoft Copilot provide the secure, enterprise-grade foundation to make that possible, combining innovation with governance and flexibility with control.
The pathway is clear… Start with a targeted use case that matters, prepare your data, and establish security and compliance guardrails. From there, scale iteratively, measure results, and refine as you go.
With the right strategy and the right partner, you can turn the promise of AI into practical, measurable impact for your teams.
Every major transformation begins with a clear vision and a trusted technology partner to make it happen. As a Microsoft Azure Expert MSP, we work side by side with business and enterprise organisations to deliver AI solutions that are secure, scalable, and aligned with strategic objectives. Contact the BUI team to get started today.
Satish Sunker and Heinrich Wewers explain why Azure Deployment Stacks are a smart next step toward greater governance and confidence in the cloud.
As cloud environments evolve and scale, managing infrastructure across multiple subscriptions, environments, and teams has become one of the most persistent challenges for IT professionals and managed service providers (MSPs) alike. The need for speed, consistency, and governance has never been more pressing and yet achieving all three simultaneously can often feel impossible.
Azure Deployment Stacks, one of Microsoft’s recent enhancements to the Azure Resource Manager (ARM) and Bicep ecosystem, aims to solve precisely that. By treating groups of Azure resources as cohesive, managed units, Deployment Stacks simplify lifecycle management and governance across complex environments without sacrificing flexibility or control.
To explore how Deployment Stacks can transform infrastructure management in Azure, we asked Cloud Solutions Architect Satish Sunker and Senior Cloud Consultant Heinrich Wewers to share their insights on what Deployment Stacks can do, why they matter, and how enterprises and MSPs can start benefiting from them.
Today’s cloud teams operate under immense pressure, says Satish Sunker. “Scaling infrastructure is no longer a nice-to-have… It’s actually an expectation from the business,” he explains. “Teams are required to provision and expand environments quickly, without compromising reliability or performance.”
With this pressure comes complexity. Maintaining consistency across environments, subscriptions, and regions can become a full-time job in itself. Each team may interpret organisational standards slightly differently or make ad hoc changes that cause divergence in the long run. “Over time, manual changes and one-off fixes can cause configuration drift from the original deployment templates,” adds Sunker. “Technical teams spend a lot of time remediating resources that are not compliant or do not meet security requirements.”
This challenge is compounded by concerns about cost management. “Teams are being squeezed to optimise spend while maintaining availability,” notes Sunker. “That often means implementing automation to dynamically scale resources up or down, which can add another layer of complexity.”
Before Deployment Stacks, many organisations relied solely on ARM or Bicep templates to deploy Azure resources declaratively. While effective for provisioning, they lacked robust lifecycle management capabilities. Once resources were deployed, keeping them in sync and cleaning them up safely was largely a manual or script-driven process.
“Enterprises want their cloud teams to be agile and manage their own infrastructure, but that can lead to inconsistencies in governance, security, and compliance. Technical debt tends to build up over time, as it becomes harder to maintain control and consistency across large environments,” says Sunker.
This is where Azure Deployment Stacks come into play.
At its core, an Azure Deployment Stack is a resource that acts as a container for multiple deployed resources, allowing them to be treated as a single, unified entity, explains Heinrich Wewers.
“Unlike a traditional ARM or Bicep deployment, which simply provisions resources, a Deployment Stack establishes a managed relationship between Azure and the resources it deploys,” says Wewers. “Azure keeps track of those resources as part of the stack, allowing for more controlled updates and cleanups.”
Behind the scenes, when a Deployment Stack is created, Azure registers a management relationship between the stack and each deployed resource. “This relationship allows Azure to track, update and clean up those resources as a single managed identity,” adds Wewers. “It ensures consistency throughout the resource lifecycle.”
The main components that make up a Deployment Stack include:
The introduction of Deployment Stacks marks an important shift in how Azure environments can be managed at scale.
“They help eliminate operational risks and reduce technical debt caused by limited control, poor lifecycle management, and lack of visibility over deployed resources,” says Wewers. “By keeping related resources grouped and tracked together, they reduce compliance gaps and ensure consistent configuration across subscriptions.”
Deployment Stacks also reduce the risk of human error. “They bring structure and predictability to how resources are deployed, updated, and cleaned up,” notes Wewers. “That’s critical for large teams working across shared environments.”
By embedding management and governance directly into the deployment process, Deployment Stacks effectively extend Infrastructure-as-Code (IaC) capabilities into the operational lifecycle. “Traditional ARM and Bicep templates are great for provisioning, but they offer limited visibility and lifecycle control once resources are deployed. Deployment Stacks enhance that process with additional management capabilities.”
The workflow for building and managing an Azure Deployment Stack follows a structured, repeatable pattern. “The first step is to identify which resource groups should be managed together as part of the same stack. This helps define clear boundaries for ownership and lifecycle management. Once the scope is set, you can use existing ARM or Bicep templates to define the resources that make up the stack. From there, Azure establishes the management relationship with each deployed resource,” explains Wewers.
When templates are changed later, Azure automatically manages updates intelligently. “When changes are made to the templates, one of two things can happen: any new resources added to the template are automatically brought under management by the Deployment Stack, and any resources removed from the template become unmanaged. Azure also allows you to define what should happen to those unmanaged resources… For example, whether they should be retained or automatically deleted.”
This makes ongoing lifecycle control more predictable and less error-prone.
Sunker highlights that Deployment Stacks integrate seamlessly into existing workflows. “You can use Azure CLI or Azure PowerShell to create and update Deployment Stacks,” he says. “In most cases, current resource deployment processes using ARM or Bicep can be seamlessly adapted to deploy and manage resources through Azure Deployment Stacks, without significant changes to existing templates or pipelines.”
However, there are a few limitations to bear in mind when working with Deployment Stacks:
These constraints are likely to evolve as the feature matures, notes Sunker, so it’s worth checking the Microsoft documentation regularly for updates.
Sunker points out that, beyond the technical capabilities, Azure Deployment Stacks deliver measurable business benefits. “From a business and operational standpoint, the biggest advantage is the increased efficiency in managing Azure resources. This efficiency translates directly into cost savings and reduced management overhead, easing the burden on cloud teams. By simplifying resource lifecycle management and improving consistency, organisations can focus more on innovation and less on maintenance,” he says.
Deployment Stacks also play a significant role in strengthening governance, consistency, and compliance across environments by reducing the need for manual actions and therefore lowering the risk of human error or oversight. “Deny settings can enforce policy and prevent engineers from making unapproved configuration changes or quick fixes that could drift from organisational standards. Because all resources in a Deployment Stack share the same lifecycle, orphaned resources are minimised, ensuring cleaner environments and easier compliance reporting.”
By combining lifecycle management with governance controls, Deployment Stacks help enterprises achieve a more secure, predictable, and compliant cloud operating model, without slowing down delivery.
Sunker also notes that Azure Deployment Stacks naturally reinforce key pillars of the Azure Well-Architected Framework, including:
This alignment makes Deployment Stacks an attractive option for enterprises pursuing well-architected cloud environments.
BUI has started adopting Azure Deployment Stacks in customer projects to address challenges observed in previous IaC implementations, particularly around configuration drift and lifecycle management, Wewers shares.
“Azure Deployment Stacks don’t replace IaC, they enhance it. By adding structured lifecycle management and governance capabilities on top of existing ARM or Bicep deployments, Azure Deployment Stacks make it easier for enterprises to adopt and scale IaC with greater confidence and control.”
Wewers gives an example: “A common scenario where Deployment Stacks deliver real value is managing proof-of-concept projects. These environments are typically short-lived, and manually tracking every deployed resource can lead to forgotten assets and unnecessary costs. With Deployment Stacks, all resources deployed during the POC are managed together. When the stack is deleted, every associated resource is automatically cleaned up.”
Deployment Stacks can also improve environment management across the development, testing and production stages, notes Wewers. “Each environment can be deployed as its own stack. This ensures environment isolation, consistent deployment, simplified lifecycle management, and clear auditability, all of which align with DevOps and governance best practices.”
Deployment Stacks are especially valuable during workload migrations or customer onboarding scenarios, he continues. “During migrations, Deployment Stacks allow you to replicate environments easily across subscriptions or regions using the same ARM or Bicep template. Temporary or transitional resources can be managed as a unit and once the migration is complete, deleting the stack safely removes all associated resources, preventing leftover costs or configuration drift. This capability helps MSPs, like us, to streamline transitions and maintain consistency from the first deployment.”
Sunker cautions that there are nuances to understand when it comes to Azure Deployment Stacks and highlights two common pitfalls.
“Mistake number one is assuming that stacks manage everything in a scope,” he warns. “Deployment Stacks only manage the resources they deploy. Any additional resources created outside the stack won’t be managed or removed when the stack is updated or deleted. Cloud teams must communicate and document which resources are under stack management and which are not.”
The second issue is overly strict Deny settings. “If Deny assignments are too restrictive, even the original deployment identity may lose the ability to manage the stack. It’s important to exclude the right service principals or admin accounts.”
Sunker’s advice? “Start small and focus on how resource management behaves before scaling to larger environments. Document your stack design and clearly define scopes to avoid confusion.”
Wewers has a similar outlook. For cloud teams ready to explore, he recommends a simple, hands-on approach: “You can use your existing ARM or Bicep templates and deploy them as a stack using Azure CLI or Azure PowerShell. Go slowly… Deploy a basic stack that includes just a few resources. Then experiment with Deny settings and the actionOnUnmanage parameters to see how Azure enforces governance and resource cleanup in practice.”
By experimenting early on, cloud teams can build familiarity and confidence before rolling out Azure Deployment Stacks across production environments.
As a Microsoft Azure Expert MSP, BUI is already helping customers identify workloads that are ideal candidates for Azure Deployment Stacks. “Our approach focuses on planning the right configuration from the start and aligning governance, lifecycle management and team workflows to leverage the benefits fully,” says Sunker.
For enterprises looking to reduce operational overhead, enhance automation maturity, and improve governance, Deployment Stacks represent a significant evolution in how Azure environments can be deployed and managed, he continues. “By turning groups of resources into manageable, lifecycle-bound entities, Deployment Stacks bring order, visibility, and control to environments that were once sprawling and difficult to standardise.”
Wewers concurs. “The benefits extend beyond the technical: Deployment Stacks simplify operations, strengthen compliance, and support a more consistent, cost-effective cloud strategy. For enterprises that depend on Azure, Deployment Stacks are a smart next step toward greater governance and confidence in the cloud,” he concludes.
As a Microsoft Azure Expert MSP, we’re here to support every stage of your cloud journey, from design and deployment to automation, security, and optimisation. Our certified architects and engineers can help you leverage innovations like Azure Deployment Stacks to streamline your infrastructure now, while laying the foundation for future growth and resilience. Contact our team to get started.
Zandre Janse van Vuuren identifies five of the most common cyberthreats and shares practical tips to help you defend against them.
By Zandre Janse van Vuuren | Service Delivery Manager: Cyber DFIR, BUI
As our world becomes increasingly interconnected through digital systems, the threat landscape for cyberattacks continues to expand. In 2024, global cybercrime costs soared to an estimated $9.22 trillion, with projections indicating a rise to more than $13 trillion by 2028.
These staggering figures highlight the need for robust security measures. Cyberthreats not only risk sensitive data, but can also disrupt operations and cause significant financial and reputational damage. Let’s take a closer look at five of the most common cyberthreats organisations face today, their potential impact, and actionable steps for mitigation.
Phishing remains one of the most prevalent cyberthreats due to its simplicity and effectiveness. Attackers often exploit human error, leveraging psychological tactics such as urgency, fear, and curiosity to trick people into revealing critical information.
Common phishing techniques include posing as trusted organisations like banks or government agencies, using realistic-looking fake websites to capture login credentials, and embedding malware in email attachments.
The rise of spear phishing (i.e., highly targeted attacks against specific individuals or organisations) has further increased the threat’s sophistication and success rate. Even tech-savvy users can fall victim if vigilance lapses, making continuous awareness and training essential.
Potential impact:
Mitigation:
With the rise of Ransomware-as-a-Service platforms, even attackers with little technical aptitude can deploy sophisticated ransomware campaigns, making this threat more pervasive than ever. These platforms provide pre-packaged ransomware tools, technical support, and even revenue-sharing models, significantly lowering the barrier to entry for cybercriminals.
Compounding the issue is the growing use of double extortion tactics, where attackers encrypt data and threaten to publicly release sensitive information unless the ransom is paid. This evolution has made ransomware one of the most concerning and financially devastating cyberthreats today, affecting organisations of all sizes across industries.
Potential impact:
Mitigation:
While external attacks often dominate headlines, insider threats can be just as damaging and sometimes more difficult to detect. Whether malicious or negligent, insiders already have authorised access to critical systems and data, allowing them to bypass many traditional security measures.
Malicious insiders may act out of financial gain, dissatisfaction, or coercion, while negligent insiders might unintentionally expose sensitive information through careless behaviour or a lack of awareness.
The dual nature of insider threats makes them particularly challenging to manage, underscoring the importance of comprehensive monitoring and regular employee training.
Potential impact:
Mitigation:
Malware attacks are often the first step in larger, multi-stage cyberattacks, serving as a gateway for attackers to establish a foothold in a target’s system. These attacks can infiltrate systems through various vectors, including compromised downloads, malicious websites, infected USB devices, phishing emails with malicious attachments, and even unsecured IoT devices.
Once installed, malware can perform a range of harmful activities, from data exfiltration and credential harvesting to deploying additional payloads for ransomware or botnet creation. The versatility and adaptability of malware make it a cornerstone of many sophisticated cyberattack campaigns.
Potential impact:
Mitigation:
As businesses increasingly rely on online services, Distributed Denial of Service (DDoS) attacks have become a favoured method for disrupting operations. These attacks flood networks or servers with overwhelming traffic, rendering them inaccessible to legitimate users.
Beyond their immediate disruptive effects, DDoS attacks are often used as a smokescreen to divert attention while attackers execute more invasive activities, such as data breaches or malware deployment.
The increasing accessibility of DDoS-for-hire services has further amplified the threat, enabling attackers to launch large-scale attacks with minimal resources or technical expertise.
Potential impact:
Mitigation:
Understanding the most common cyberthreats is crucial for safeguarding your organisation. Phishing, ransomware, insider threats, malware, and DDoS attacks each present unique challenges, but proactive measures such as employee training, robust technical defences, and regular updates to security protocols can mitigate their impact.
Cybersecurity is a continuous effort that demands vigilance, adaptation, and a culture of awareness. You can protect your business assets, maintain trust, and ensure resilience in an ever-changing threat landscape by staying informed and prepared.
The 2025 Data Privacy Week awareness campaign aims to educate and empower individuals to take control of their personal data.
BUI is proud to announce its commitment to the 2025 Data Privacy Week campaign. As a Data Privacy Week Champion, BUI recognises and supports the principle that all organisations share the responsibility of being conscientious stewards of personal information.
Data Privacy Week is an annual awareness initiative that takes place from 27-31 January. The goal is twofold: to help individuals understand that they have the power to manage their data and to help organisations appreciate why it’s necessary to respect the user data they collect, process, and store.
This year’s theme is Take control of your data – and it’s a timely reminder for everyone as the world becomes more digitally connected, notes BUI Group Governance and Compliance Manager Dhiren Boodhia. “Data Privacy Week highlights the fact that trust is built on transparency. Individuals want to know that their personal information is respected and protected by those who have access to it,” says Boodhia. “As privacy laws and public expectations continue to evolve, organisations should strive to go beyond mere compliance to create a culture of accountability around data privacy and security.”
Your digital activities generate huge amounts of data: websites, apps and online services collect information about your behaviours, your interests, and your purchases. Often, this includes personal data like your identity number and home address. It can even include data about your physical self: think about how smart devices can save health and fitness records as you exercise.
While you cannot control how each byte of data about yourself and your family is shared and processed, you are not helpless! In many cases, you can control how you share your data with a few simple steps. Remember, your personal data is precious and you deserve to be selective about who you share it with. Here are three simple steps to help you manage your data privacy, according to guidelines from the National Cybersecurity Alliance:
Nowadays, when you download a new app, create a new online account, or join a new social media platform, you’ll often be asked for access to your personal information before you can even use it! This data might include your geographic location, contacts, and photos.
For these businesses, personal information about you is tremendously valuable – and you should think about whether the service you get in return is worth the data you must hand over, even if the service is free. Make informed decisions about sharing your data with businesses or third-party service providers… Ask yourself:
For every app, account, or device, check the privacy and security settings. These should be easy to find in the relevant Settings section and should take a few moments to change. Set them to your comfort level for personal information sharing. In general, it’s wise to share less data, not more.
You don’t have to do this for every account at once: start small and over time you’ll make a habit of adjusting all your settings to your comfort level. The National Cybersecurity Alliance has several free resources, including the Manage Your Privacy Settings page, to help you find and check the settings of social media accounts, apps, and more.
Data privacy and data security go hand-in-hand. Along with managing your data privacy settings, remember these four tips to safeguard your information:
During Data Privacy Week this January, we’ll be sharing useful tips and resources to help you become more aware about data privacy at work, at home, and on the move. Follow us on Facebook and LinkedIn so you never miss a post, and join the conversation by using the #DataPrivacyWeek hashtag online.
About Data Privacy Week
Data Privacy Week began as Data Privacy Day in the United States and Canada in January 2008 as an extension of the Data Protection Day celebration in Europe. Data Protection Day commemorates the 28 January 1981 signing of Convention 108, the first legally binding international treaty dealing with privacy and data protection. The National Cybersecurity Alliance, the United States’ leading non-profit, public-private partnership promoting cybersecurity and privacy education and awareness, leads the effort in North America each year. For more information, visit www.staysafeonline.org/data-privacy-week/.
About the National Cybersecurity Alliance
The National Cybersecurity Alliance (NCA) is a non-profit organisation on a mission to create a more secure, interconnected world. The NCA advocates for the safe use of all technology and educates everyone on how best to protect themselves, their families, and their organisations from cybercrime. The NCA creates strong partnerships between governments and corporations to amplify its message and to foster a greater digital good. For more information, visit www.staysafeonline.org.
In Part 2 of our spotlight series on incident response, Zandre Janse van Vuuren explains how to create a comprehensive Incident Response Plan for your organisation.
By Zandre Janse van Vuuren | Service Delivery Manager: Cyber DFIR, BUI
In Part 1, we highlighted the importance of having an Incident Response Plan (IRP) to minimise damage, reduce recovery time, and secure sensitive data during a cybersecurity incident. Now, let’s dive into how to create an effective IRP for your organisation, with practical, step-by-step guidelines you can follow.
The foundation of any effective IRP begins with setting clear objectives and defining the scope. Objectives help align your incident response efforts with your organisation’s goals, risk tolerance, and regulatory requirements. Typical objectives include:
The scope defines the types of incidents the IRP covers and may vary depending on industry standards or regulatory guidelines. For instance, a healthcare provider may need a specific scope for protecting patient data, while a financial institution may focus on transaction security and fraud prevention. By establishing scope early on, you can ensure that your IRP is comprehensive yet focused.
An IRP functions best when it has a well-structured team with clear roles and responsibilities. The team may include internal stakeholders, like IT and management, and external stakeholders, such as legal consultants or third-party security experts.
Each member of your incident response team should have a clearly defined role to prevent delays and confusion during an incident. Roles may include:
Designating these roles upfront helps the team respond more efficiently and cohesively during an incident.
Incidents can range widely in scope and severity, from minor phishing attempts to full-blown data breaches. To streamline response efforts, you must categorise potential incidents and assign impact levels to each. Incident categories could include:
Each category should have multiple impact levels (e.g., low, medium, high) based on criteria like the number of affected systems, potential data loss, and the severity of business impact. This prioritisation ensures critical incidents receive immediate attention, while lower-priority events are handled appropriately without over-allocating resources.
Timely detection and reporting are crucial for an effective IRP. Make sure you implement security tools and monitoring systems that can detect unusual activities or potential threats. There’s a wide range of endpoint protection platforms, network monitoring tools, and intrusion detection systems available for business and enterprise organisations.
Once an incident is detected, a notification protocol outlines how and when incidents should be reported internally and externally.
Make sure you clearly define the people or parties to be notified, the method of notification, and the relevant timeframe.
Containment and eradication are central to limiting an incident’s impact and preventing further damage. Document your procedures for both short-term and long-term containment and eradication.
Both containment and eradication should be documented in detail, tailored to specific incident types, and tested to confirm that they are feasible and effective.
Once the incident is contained and eradicated, recovery efforts aim to return systems to regular operation safely and reliably. The recovery phase may involve restoring affected systems, verifying data integrity, and assessing system functionality. A critical part of this step is to monitor your systems for any indication that the incident may recur, ensuring any residual threats are eliminated.
Remediation actions may also include taking preventative steps, such as reinforcing security controls, updating policies, or providing additional employee training. Documentation is essential here, as lessons learned in recovery and remediation will help improve your IRP over time.
Communication during an incident is essential to inform all stakeholders, control potential reputational damage, and fulfil legal obligations. Your communication strategy should differentiate between internal communications, which provide regular updates to relevant staff, and external communications, which may include notifying customers, partners, regulatory bodies, and the media.
Effective communication strategies often use predefined templates and include guidelines for customising messaging based on the nature and impact of the incident. Designate a spokesperson from your communications or public relations team to ensure consistency and accuracy in your external messages.
Every incident provides a learning opportunity. The post-incident review process aims to evaluate the IRP’s performance, identify areas for improvement, and ensure that lessons are incorporated into the IRP for future incidents.
This step typically includes:
A robust post-incident review process strengthens the IRP and demonstrates a commitment to continuous improvement, which is critical for fostering a proactive security culture and maintaining regulatory compliance.
Bonus tip! The success of any IRP is closely tied to the response team’s performance during high-pressure situations – and that’s why it’s important to cultivate the right mindset. If you and your teammates can maintain your composure, think objectively, and work in unison, then you’ll be ready when it matters most.
With a comprehensive IRP and a teamwork mindset, your organisation will be better equipped to navigate security incidents. Download our checklist to guide you in creating your IRP.